Hackers are becoming increasingly better at tricking unsuspecting computer users into clicking on the bogus phishing emails the hackers send that are meant to plant viruses/bots, steal data, hold their files for ransom or worse steal identities or bank/credit card info. What’s worse is that the everyday law firm staffer who’s just trying to do their jobs fall victim far too often causing their firms severe financial loss and the potential for the lawyers they work for to be censured or much worse. As a law firm staffer, associate or partner you have a responsibility to educate yourself on how to avoid cyber threats including common phishing attempts.
“Phishing” is the attempt to obtain sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money) by masquerading as a trustworthy entity in an electronic communication.
Use and share this simple checklist to help you and your colleagues recognize and avoid Phishing emails:
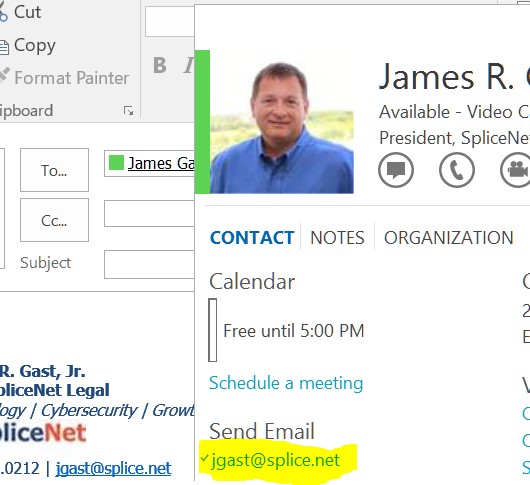
Actual Email Address
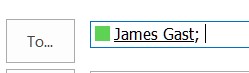
1. The “To:” Line: There are two elements to the To: line. First is the way it looks (the Display Name) and the second is the actual email address. Many email programs only show the Display Name and mask the email address. Some will show the Display Name and email address next to each other. However, in either case by hovering over the Display Name the underlying email address is shown. A strange email address can help spot a phishing scam.
2. Subject Line: Subjects lines are hard to use to spot a phishing email because even the most professional staffers often use very casual language as their email subjects. Nevertheless keep an eye open for crazy subjects or poor language structure in the subject line. They can sometimes help lead you to look for other elements in this checklist.
Display Name
3. Proper Language: improper language use can be a huge help to spot a trick. Look for misspellings, bad grammar or incorrect sentence structure. Many hackers just use an online Translator site to convert their email messages into English. Fortunately these Translators leave a lot to be desired and don’t always get it right.
4. Incorrect symbols and/or their use:
A. 40.00$ instead of $40.00
B. 21th instead of Feb 21st
C. Date structures like 20/2/2017 instead of 2/20/2017
5. Attachments: BE VERY CAUTIOUS HERE! If you are not expecting an attachment, as a verification call the person or CREATE/SEND A NEW EMAIL to them typing their known email address yourself. Do not respond to the email asking for verification. The hacker will likely be very happy to respond letting you know that it’s a legit email and attachment.
6. Web Links: these are very tricky because they look legit but they’re just like the To: line. They can display one thing and be something very different. DO NOT CLICK on a suspect web link to test it. Hovering over it will almost always (not in every case) show the links actual web site destination. If you don’t know what it is, DON’T CLICK IT.
7. Phone Numbers: sophisticated hackers are including phone numbers that get you to “call for validation” of their email or some info in their email. Don’t fall for it. You’d be better off calling for pizza.
Hackers are using every phycological, brain game trick they can to lower your alertness to get you to click without thinking in that first, weak split-second when your eyes and mind haven’t communicated yet. They know that the eye-to-hand muscle reaction process much faster than the eye-to-mind-to-thought process and all they need is that millisecond for you to click before you think. Don’t fall prey. Commit the simple checklist to memory and use it when you read your email. Soon your hand-eye reaction speed will be controlled by your “threat instinct” and you won’t be fooled again.